BAM!
There it is. Right in your face one morning when you check your social feed as news.
That nasty little something that someone, a bot, or a person, or maybe both left for you overnight. It is a digital take down. A bad blog post. A social media meme that is being unanswered or purposely pumped up to discredit you, your company or organization or your brand. Or maybe it is a false allegation. Or paid fake bad reviews that your competitors put up. Or even worse a combination of all the above; plus a malware or trojan laden url embedded in it.
Face it. The Internet is a hostile place for your reputation and your brand; whether that is personal, corporate or government. The control and management of your cyber security, reputation management; and social media appearance start and end with you.
It is 2015 and it is worth paying attention to, in fact it is important to take stock of your online reputation. The management of it, and the control of it, is yours. Not anyone else. True for cyber security, your safety on social media and how they are all connected. Here is an older post that pointed this out in 2010. Also a more recent (2014) look of the correlation between cyber security, reputation management and social media is here.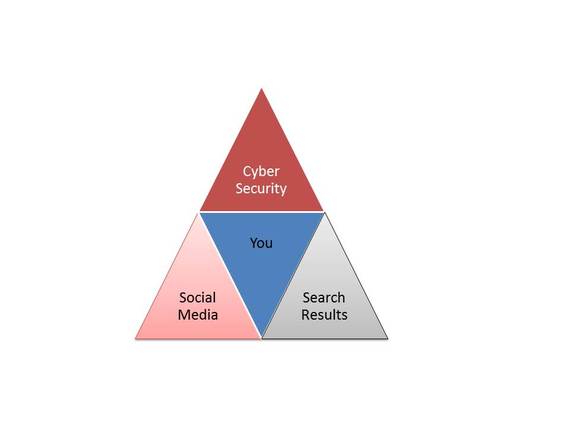
The Internet, social media, the cloud, mobility, bring your own device, artificial intelligence, autonomous computing etc etc -- all are really cool buzz words. All come with a price to pay. Cyber security, that of yours, your company and your family. Loss of privacy through social media tracking and people following your every move. Loss or defacement of your online reputation. This translates to loss of your future reputation too.
My company Digijaks offers boutique solutions for high impact individuals, brands and organizations to deal with the combination of cyber security, social media and reputation management and control. We gave the following pointers to our clients at the end of last year, as a self checklist:
Our top 10 List of Ways That Cyber Security, Social Media and Reputation Management and Reputation Control all mesh together.
- Social Media -- is the entrance point for viruses, malware, malformed links, phishing and learning enough about someone to turn around and destroy their reputation.
- Mobility -- allows for instant access to social media, email, sms, cloud and phone, and video, as ways to tear down a brand or reputation. It can happen anywhere, at any time, by anyone around you holding a smartphone or smart watch or smart glasses.
- Cloud -- allows people to store information quickly and easily. This can be for phishing, for cyber crime, for reputation destroying or extortion. Images and videos, poems and documents and your complete online profile can be easily harvested by smart people and or bots and then turned around against you. What information are you allowing out or putting out to make it easier to be attacked? Or easier to have your reputation tarnished or that of your brand?
- Bring Your Own Device (BYOD) -- While fun and easy for users and your employees BYOD brings a whole fruit basket worth of cyber security and reputation management and control issues along with it. BYOD allows users and employees to access the internet and social media channels without approval or notice from the employer. A reputation can be destroyed in an instant with a recorded conversation, a video, an errant email or sms, or worse corporate espionage and cyber crimes can be instituted easily with BYOD.
- Artificial Intelligence -- The name alone. What does it mean? How can artificial intelligence (AI) bots or autonomous computing affect your cyber security and reputation management and control? In so many ways we are just beginning to understand.
- Lazy People -- Sorry but many times the malware or the phishing or the destruction of reputation starts with someone simply being lazy, not having security and privacy settings attended to, and or worse letting someone else use their login credentials.
- Your Competition -- They have access to the same tools you do. They can buy hackers, they can buy reputation destruction; they can attempt to steal your trade secrets; they will try to insert bad people into your organization at every level. (See 8 below.)
- Bad People -- No good, no ethos or morals. These people do not care if they harm you. They seek to. These come in the form of social media contacts or email phishing all the way through HR, interviewing, shadowy financiers and content theft propagators from online goods. They will use any and every tool out there to disrupt your business, to destroy your reputation.
- Posting stupid pictures of yourself -- on to any website regardless of how safe you *THINK* it is.
- Not checking the health and welfare of your own digital reputation and brand.