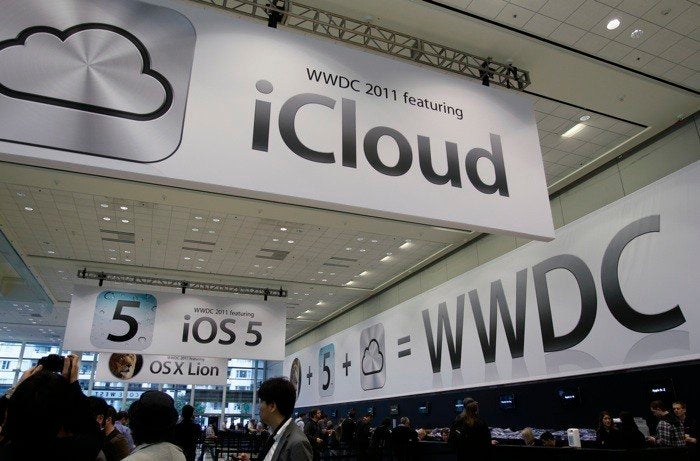
When Apple announced its iCloud service, commentators spilled much ink wondering if the data of users would be safe from hackers. But an equally important angle to the story was ignored: whether the data in the cloud has enough legal protection to keep it from the prying eyes of the government.
Embrace of the cloud -- moving corporate or personal data and its processing into service provider data centers -- is hardly restricted to Apple. Companies such as Google, Microsoft, and salesforce.com have been providing cloud-based services to businesses and consumers for many years. Earlier this year, Amazon announced its CloudDrive for stored music and other files; a few weeks ago, IBM announced its SmartCloud for education services. These companies and others want to offer their customers the improved performance and convenience that comes with the cloud paradigm.
Under current law, however, data stored in the cloud is less protected against government overreaching than data stored locally. That is, except in the four states covered by the sole federal appeals court to rule that data stored in the cloud is protected by the Fourth Amendment's rule against unreasonable searches and seizures, requiring a warrant issued by a judge. And maybe not on the West Coast, where the federal appeals court has held that some communications in the hands of service providers -- specifically stored text messages -- are protected. But that ruling was set aside by the Supreme Court on other grounds. A crazy quilt of statutory provisions and judicial decisions leaves potential cloud users uncertain and puts service providers in the uncomfortable position of deciding when to comply with a government request for user data and when to fight it in court.
Yes, the security concerns about cloud computing are valid -- the recent hacks of Google accounts belonging to government officials are just one example -- but security in the cloud should not be as controversial as commentators have suggested. Cloud computing does not require entirely new security schemes as much as it does a religious application of time-tested tools and practices. We know how to encrypt connections, and identity solutions are available to authenticate users. Careless implementation and the human factor remain the key sources of vulnerability, but that is true whether data is stored locally or remotely. Indeed, the cloud offerings of major companies are more secure than those paper files at a hospital or the unencrypted data on a laptop.
The picture is very different, however, when the government comes calling. Locally stored data, whether printed out and placed in a filing cabinet or stored on your personal hard drive, is subject to Fourth Amendment protections, and government agents cannot come in and seize it unless they have a warrant issued by a judge based on probable cause. But the U.S. Justice Department argues that you surrender your Constitutional rights when you store that very same data with a cloud service provider. Under the government's view, a cloud service provider can be forced to disclose whatever it has with a mere subpoena, issued by a prosecutor or an FBI agent, with no approval by a judge and without any reason even to suspect the record subject to be involved in criminal conduct. Digital data deserves the same checks and balances long applied in the offline world.
Ultimately, I believe, the Supreme Court will reaffirm that the Fourth Amendment protects people, not hard drives, but that could take years if not decades. (After the Supreme Court ruled in 1928 that telephone conversations were not protected by the Constitution, it took nearly 40 years for the Court to reverse itself and say that wiretapping was a search and seizure subject to the standards of the Fourth Amendment.) The courts tend to move very slowly in addressing new technologies.
For prompt action, the key lies in reforming the Electronic Communications Privacy Act, or ECPA. Adopted in 1986, ECPA helped spur the growth of email and the mobile phone industry by statutorily extending the Constitution's warrant requirement to the real-time interception of email and wireless phone calls. But in 1986, Congress did not anticipate the significance of the cloud. Instead, ECPA says that email loses its strong privacy protection after it has been in storage for 180 days. (The Justice Department says that once you've read an email, it can be accessed immediately without a warrant. This leads to the head scratching realization that the unopened junk mail in your spam folder may have more protection than your read-and-re-read electronic love letters.) Moreover, files that you yourself store in the cloud never enjoy the protection of the warrant standard; under the statute, they are available to the government with a prosecutor's subpoena from the moment they are uploaded.
There is growing evidence that the ease with which government agencies in the U.S. can access information stored in the cloud is posing a serious problem for American companies trying to woo foreign clients. Perry Robinson, Associate General Counsel of Rackspace, told a congressional panel last year that he spends a "good deal of time" each week explaining to potential customers "basically all over the world ... exactly what circumstances in which their data may be accessed" by U.S. law enforcement officials.
It is clearly time to update the law to ensure the application of Fourth Amendment standards to all private content, regardless of the technology or business model used to store it. A broad coalition of technology companies, privacy advocates, conservatives and think tanks have called on Congress to do precisely that. Moreover, the initial author of ECPA, Sen. Patrick Leahy has himself concluded that the law is now outdated and he has introduced legislation to reform ECPA and require a warrant for government access to proprietary or private data stored in the cloud.
New technology, the traditional warrant. Let's give cloud-based services the legal protections they deserve and their users expect.
